Employee theft accounts for $26 billion in annual retail losses, representing 29% of total shrinkage (Source: Appriss Retail). The bulk of that loss doesn't happen in stockrooms or loading docks. It happens at the register—through sweethearting, skip-scanning, fraudulent refunds, and void manipulation. These transactions look perfectly normal on camera. A cashier scans items, a customer pays, the drawer closes. Nothing appears wrong.
That's the gap. Traditional camera systems record what happened, but they don't help your team prove what actually happened at the register. A void looks like a void. A refund looks like a refund. Without linking video to the transaction data behind it, loss prevention teams are left scrubbing hours of footage to reconstruct a case that POS data could have flagged in seconds.
This article breaks down the most common forms of register fraud, explains why they evade standard video review, and walks through how POS video integration and exception-based reporting let LP teams flag anomalies, verify them with time-stamped footage, and close investigations faster—without adding headcount.
Key terms to know
Before examining detection methods, a few definitions are worth clarifying. These terms describe the specific fraud types and detection approaches covered throughout this article.
Term | Definition |
|---|---|
Sweethearting | A cashier processes a transaction at a reduced price—or skips items entirely—for a friend, family member, or favored customer. The register shows a completed sale, but the store absorbs the difference. |
Skip-scanning | A customer at self-checkout places an item in the bagging area without scanning its barcode, resulting in a lower total. |
Exception-based reporting (EBR) | A method where POS systems automatically flag transactions that deviate from defined policies or statistical norms—excessive voids, unusual refund patterns, no-sale drawer openings—rather than requiring manual review of every transaction. |
POS video integration | The practice of linking point-of-sale transaction data to corresponding video footage so that each flagged exception is paired with a time-stamped clip from the register camera. |
No-sale transaction | A cash drawer opening without any sale being processed through the register. |
Why register fraud stays invisible to standard camera systems
How does a cashier steal hundreds of dollars a week without anyone noticing on camera? The answer is simple: register fraud is designed to look like a normal transaction.
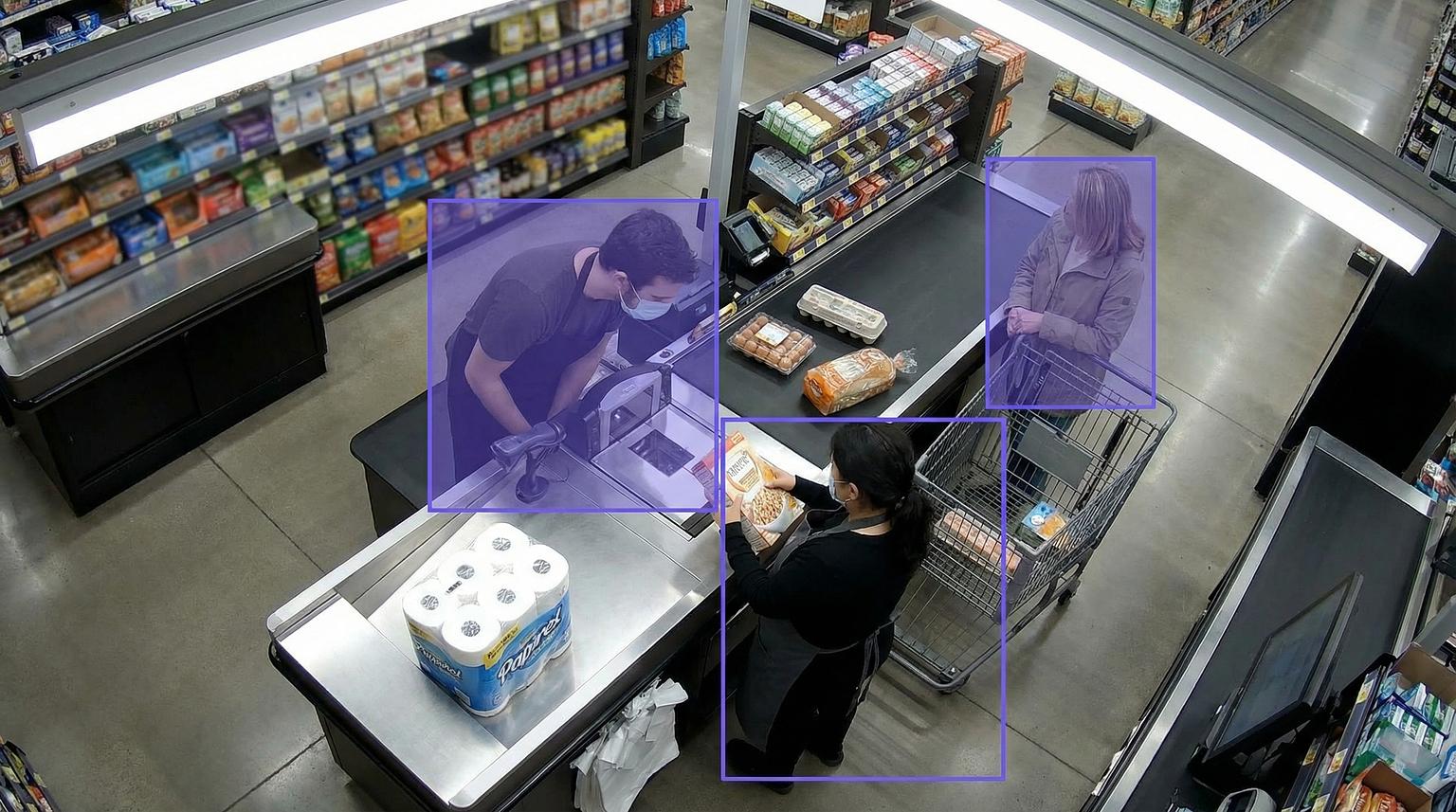
When an employee sweethearts at the register, they scan one item and bag three. The camera shows a routine checkout. When a cashier processes a refund for merchandise that was never returned, the footage shows someone standing at a register pressing buttons. When a self-checkout customer skip-scans a high-value item, the video shows a shopper bagging groceries.
None of these behaviors trigger a visual alarm. The fraud lives in the data—in the gap between what was scanned and what left the store, between what was refunded and what was actually returned. Only 10.9% of employee theft losses are recovered through apprehension-based approaches, meaning most internal theft accumulates undetected until it surfaces in loss reports (Source: Pygmalios).
For regional LP teams covering dozens of locations, the time cost adds up fast. Reviewing even one suspicious shift across a single store can consume hours of footage scrubbing. Multiply that across 30 or 40 stores, and the investigation backlog grows faster than any team can clear it.
The five most common types of cash register theft
Register fraud takes several distinct forms, each with a different detection signature. Understanding these patterns is the first step toward building a targeted response.
Fraud type | How it works | What the POS data shows | What the camera shows |
|---|---|---|---|
Sweethearting | Cashier scans one item but bags several, or applies unauthorized discounts for friends/family | Discounts clustered around specific shifts or employees; price overrides without manager authorization | Normal-looking checkout—nothing visually suspicious |
Skip-scanning | Customer at self-checkout places items in the bagging area without scanning | Weight discrepancy between scanned items and bagging area; lower-than-expected basket totals | Shopper bagging items—indistinguishable from legitimate behavior |
Refund fraud | Employee processes a return for merchandise never purchased or never returned | Refunds without receipts; refund-to-sales ratios far above peer averages; refunds processed with no customer present | Someone at a register pressing buttons—no visible merchandise exchange |
Void manipulation | Cashier voids a legitimate sale after the customer pays, then pockets the cash | Void counts significantly above peer averages; voids clustered at shift end | A completed transaction followed by register activity—easy to miss |
No-sale drawer access | Employee opens the cash drawer without processing any transaction | Repeated no-sale events logged under one employee ID; frequency far exceeding peers | Drawer opens, hand enters—could be making change or could be theft |
Each of these fraud types shares one trait: the video alone doesn't tell the story. The evidence lives at the intersection of transaction data and footage.
How exception-based reporting flags register fraud automatically
The traditional approach to catching cash register theft—reviewing daily reconciliation reports and then hunting through footage—operates on a lag. By the time a $200 discrepancy surfaces, the trail is cold. Exception-based reporting flips this workflow. Instead of reviewing every transaction manually, the POS system flags deviations from policy or statistical norms and surfaces them for targeted review (Source: Heksia).
Here's what a well-configured EBR system monitors:
Excessive void transactions. A cashier who normally processes two voids per shift but suddenly logs twelve triggers a same-day alert, enabling timely investigation rather than discovery during a quarterly audit (Source: Petrosoft).
Refunds without proper documentation. When the same employee processes multiple no-receipt refunds to the same payment method, or refund amounts cluster around shift changes, the system surfaces the pattern for review.
No-sale drawer openings. If one employee opens the register as "no-sale" twenty times per shift while peers rarely use the function, that frequency gap signals a potential theft pattern (Source: Petrosoft).
Unauthorized price overrides. When a $49.99 item rings at $25.99 without manager approval, the system flags the override, the employee, and the product category (Source: Heksia).
Disproportionate refund-to-sales ratios. When one cashier's refund volume far exceeds their sales volume compared to peers, the statistical anomaly surfaces without anyone needing to manually spot it (Source: Appriss Retail).
The payoff is faster verification and fewer wasted review hours. Rather than LP teams spending hours combing through transaction logs, the system delivers specific transactions, specific employees, specific times, and specific patterns—automatically.
Linking video to POS data: the "confirm and investigate" workflow
Exception-based reporting identifies what looks suspicious. POS video integration answers what actually happened.
When a POS exception alert fires—say, five refunds totaling $847 on a single shift—the system retrieves the corresponding video footage from that checkout lane at those exact timestamps. The LP manager reviews five specific clips, not hours of checkout area footage (Source: Petrosoft).
This integration gives LP a repeatable "flag, verify, document" workflow:
The EBR system detects an anomaly (e.g., excessive voids from Cashier #3).
The platform automatically links each flagged transaction to time-stamped video from the corresponding register.
The investigator reviews only the relevant clips—confirming whether a customer was present, whether merchandise was exchanged, or whether the transaction was legitimate.
Verified incidents are documented with time-stamped evidence, creating a shareable case file.
Here's the difference: a cashier processes a refund, but the linked video shows no customer at the register at that timestamp. That single clip confirms the refund was fraudulent—a conclusion that would have taken hours of manual footage review to reach.
One convenience store operator using integrated loss prevention analytics reported compressing investigation time from hours of checkout footage review to minutes of targeted clip review (Source: Petrosoft). For a regional manager covering dozens of locations, that efficiency gain means more cases investigated without adding investigator headcount.
Skip-scan detection at self-checkout
Self-checkout environments present a distinct set of hurdles because employee involvement is minimal, but customer fraud—skip-scanning, barcode switching, item concealment—is widespread. Research on self-checkout shrinkage found that 71% of loss cases involve hiding items behind or under other items, 52% involve barcode switching, and 49% involve item pass-around schemes (Source: Blue Star).
Effective skip-scan detection layers multiple signals together:
Detection layer | What it catches | Limitation when used alone |
|---|---|---|
Weight verification | Items placed in bagging area that don't match expected weight of scanned items | Generates false positives that frustrate legitimate customers |
Computer vision | Item concealment, barcode switching, scanning one item while bagging another | Requires tuning to reduce noise in high-traffic environments |
Transaction analytics | Basket totals significantly below expected averages for item count | Can't distinguish between deal-seeking and fraud without visual confirmation |
When these layers work together, the system can trigger a staff assist prompt—asking the customer to rescan—without turning it into a confrontation. This "gentle friction" approach maintains the customer experience for legitimate shoppers while intervening when suspicious behavior is detected.
Walmart employees have adopted a tactical version of this approach: when suspicious self-checkout behavior is detected, staff can remotely freeze the transaction, requiring assistance before the customer can proceed (Source: Marca). The technology helps stores intervene without adding more self-checkout labor.
How All Star Elite cut cash shrink from 6% to 1%
All Star Elite, a multi-location sports apparel retailer with 80 U.S. shopping-center stores, faced significant cash and merchandise shrink before deploying Spot AI's unified video platform with analytics.
The results were measurable:
Cash shrink dropped from 6% to 1%—an 83% reduction—after deploying Spot AI's POS integration and video analytics across locations.
Investigation efficiency improved by more than 50% through centralized case workflows, where video clips are attached and annotated directly within the platform.
Law enforcement case timelines compressed from 2–3 months to approximately 1 month, thanks to shareable, time-stamped evidence packages.
Incident resolution time dropped from hours to minutes using video AI search to locate specific transactions and behaviors.
Beyond loss prevention, All Star Elite used people counting and performance dashboards to optimize store operations—reporting 5–15% sales increases from product-placement changes and closing three underperforming stores before absorbing another year of losses (Source: Spot AI customer story).
For LP teams managing multiple locations, this case illustrates a key principle: when video and POS data are unified in one platform, your team can verify exceptions fast and build cases that hold up—without adding headcount.
Building POS governance that reduces fraud opportunity
Technology identifies fraud patterns, but operational controls make fraud harder to commit in the first place. The most effective approach embeds segregation of duties directly into POS workflows so that no single employee can execute, approve, and reconcile transactions without oversight (Source: Heksia).
Key POS governance controls include:
Refund thresholds. Refunds above a defined amount (e.g., $25 or $50) require manager approval before processing, creating a visible record of authorization.
Price override accountability. Overrides require a manager discount code or password, tying every price change to a specific approver.
No-sale logging. Every no-sale drawer opening is logged with employee ID and timestamp. Frequency reports surface abuse patterns.
Void sign-off. Voids require manager review—either in the moment or through daily void reports that highlight outliers.
These controls aren't punitive. They're designed to raise the threshold for fraud by requiring a second person's involvement. When honest employees see that the system is structured to deter misconduct, compliance becomes the default behavior.
Considerations and limitations
No system catches everything, and any exception-based approach requires careful calibration to be effective.
Alert fatigue is real. If thresholds are too sensitive, the system generates excessive false positives and managers start ignoring alerts. Initial tuning periods—where the system runs in observation mode before requiring action—help organizations calibrate thresholds against their own historical data.
Human judgment remains essential. A spike in voids could indicate fraud or a legitimate product recall. The system surfaces the anomaly; the investigator determines the cause. Training must emphasize fair investigation practices and discourage confirmation bias (Source: Paradigm IE).
Investigation protocols protect the organization. Proper documentation, HR and legal counsel involvement before confrontation, and allowing employees to provide context are all necessary steps. Improper investigations can expose organizations to liability (Source: Paradigm IE).
Tuning is iterative. As investigators provide feedback on which alerts proved actionable, the system adjusts thresholds to improve signal-to-noise ratios over time.
Turning register footage into a loss prevention force multiplier
Register fraud persists because it hides in plain sight—inside transactions that look normal on camera but tell a different story in the data. Sweethearting, skip-scanning, void manipulation, and refund fraud all share the same trait: they're invisible to video alone and buried in noise when you only look at POS data.
The path forward connects both. Exception-based reporting flags the anomalies. POS video integration pairs each flag with time-stamped footage. And advanced search capabilities compress investigation time from hours to minutes—letting LP teams cover more stores, close more cases, and build stronger evidence without growing headcount.
Spot AI's unified video AI platform connects to existing cameras and POS systems, surfaces POS exceptions with linked video, and delivers searchable, time-stamped evidence through a single cloud dashboard. The system can be live in under a week, working with your current infrastructure—no rip-and-replace required.
"When I show managers the video evidence of unsafe practices, they get it immediately. It's not just me telling them there's a problem - they can see it for themselves."
Kevin, Unique Industries (Source: Spot AI customer story)
If LP teams need a faster way to go from a POS exception to time-stamped video evidence, request a demo to see how Spot AI's AI Agents help teams flag, verify, and document register fraud in a single workflow. You can also explore the All Star Elite customer story to see how one 80-store retailer cut cash shrink by 83%.
Frequently asked questions
What are the best practices to prevent cash register theft?
The most effective approach combines operational controls with technology. On the operational side, implement segregation of duties so no single employee can process, approve, and reconcile transactions. Require manager authorization for refunds above a set threshold, log every no-sale drawer opening with employee ID and timestamp, and mandate sign-off on voids. On the technology side, deploy exception-based reporting to automatically flag transactions that deviate from policy or statistical norms, and integrate POS data with video so flagged exceptions are paired with time-stamped footage for rapid verification.
How can retailers detect employee theft at the register effectively?
Exception-based reporting is the foundation. Configure your POS system to monitor for excessive voids, no-sale drawer openings, unauthorized price overrides, refunds without documentation, and disproportionate refund-to-sales ratios by employee. When these exceptions are linked to corresponding video clips, investigators can verify whether a flagged transaction was legitimate or fraudulent in minutes rather than hours. The key is moving from manual reconciliation reviews to automated anomaly detection that surfaces the highest-probability cases first.
What is sweethearting and how can it be detected?
Sweethearting occurs when a cashier processes a transaction at a reduced price—or skips scanning items entirely—for friends, family, or favored customers. The store absorbs the difference. Detection relies on POS analytics that identify patterns: discounts clustered around specific employees or shifts, price overrides without authorization, and transaction totals that consistently fall below expected averages for the items being purchased. Video integration confirms the behavior by showing whether items were bagged without being scanned or whether unauthorized discounts were applied during the transaction.
How does POS video integration help with loss prevention?
POS video integration links every transaction event—voids, refunds, no-sale drawer openings, price overrides—to the corresponding video footage from that register at that timestamp. When an exception-based reporting system flags a suspicious transaction, the investigator doesn't need to search through hours of footage. The system delivers the specific clip tied to that specific event. This compresses investigation time significantly and produces time-stamped, documented evidence that supports internal case building and law enforcement coordination.
What technologies are available for register fraud detection in 2026?
The current technology stack for register fraud detection includes exception-based POS reporting (which flags transaction anomalies automatically), video AI analytics (which enable searchable footage by attributes like clothing color, time, or register location), POS-to-video integration (which links flagged transactions to corresponding clips), and self-checkout monitoring systems that combine weight verification with computer vision to detect skip-scanning and barcode switching. The most effective implementations layer these technologies together and connect them through a unified platform, allowing LP teams to move from alert to verified evidence in a single workflow.
About the author
Sud Bhatija is COO and Co-founder at Spot AI, where he scales operations and GTM strategy to deliver video AI that helps operations, safety, and security teams boost productivity and reduce incidents across industries.
























.png)
.png)
.png)
.svg)